News of data breaches are an almost daily occurrence, with terrifying revelations of major brands exposing all kinds of personal information. It can take different forms, like an Elasticsearch database being left open to the internet, as we’ve seen twice this week (57 million US citizens and 32 million users of SKY Brazil), or a total network breach like we saw with Marriott’s 500 million Starwood members.
I’m not here to shame these organizations, but in less than one week we’ve seen nearly 600 million user records stolen or leaked, including postal addresses, passport data, company information, and email addresses, to name just a few.
First things first, companies need to understand their obligation to preserve whatever data they have and how it was accessed, and report this to proper authorities and regulators when user data is compromised. Understand your organization’s responsibilities in the various jurisdictions in which you operate. For example, GDPR has a 72-hour notification requirement, Canada just started mandatory notification on Nov 1, and Australia’s 2017 changes to Mandatory Breach reporting where both indicate notification is within a reasonable time frame.
This blog won’t detail the whole process for investigating and closing a breach—This is something that will be tailored to each business, and there are experts specializing in this area. What I will cover, though, is how to notify your impacted users of a data breach while minimizing the impact to your brand’s email and IP reputation.
Let us quickly do a reality check here: A huge email distribution to notify users of a breach will have a reputation impact, regardless of how you notify people. You are going to get complaints, you are going to hit spam traps, you are going to have an increase in customer service issues. But there are a number of things you can consider to hopefully lessen the long-term impact.
Communication Channels: If you plan on sending email notifications, work closely with your email service provider’s (ESPs) team to figure out the best course of action and the necessary steps to take to reduce your risks. They may have a process in place to help mitigate some of these reputation issues already. This could mean they will begin by notifying the larger email community (i.e., mailbox providers (MBPs) and blocklist providers) in advance of sending these messages or they may have alternative IPs you could access. Remember, email doesn’t have to be your only communication method. Yes, email is the fastest and most affordable in the short-term, but living in the spam folder for a couple months might have a larger impact on your bottom line than would using multiple channels. Consider postal mail for your higher-risk segments, such as bounced and unsubscribed users, or perhaps use alternative methods of communication such as site pop-ups, in app messages, or account notifications upon log-in.
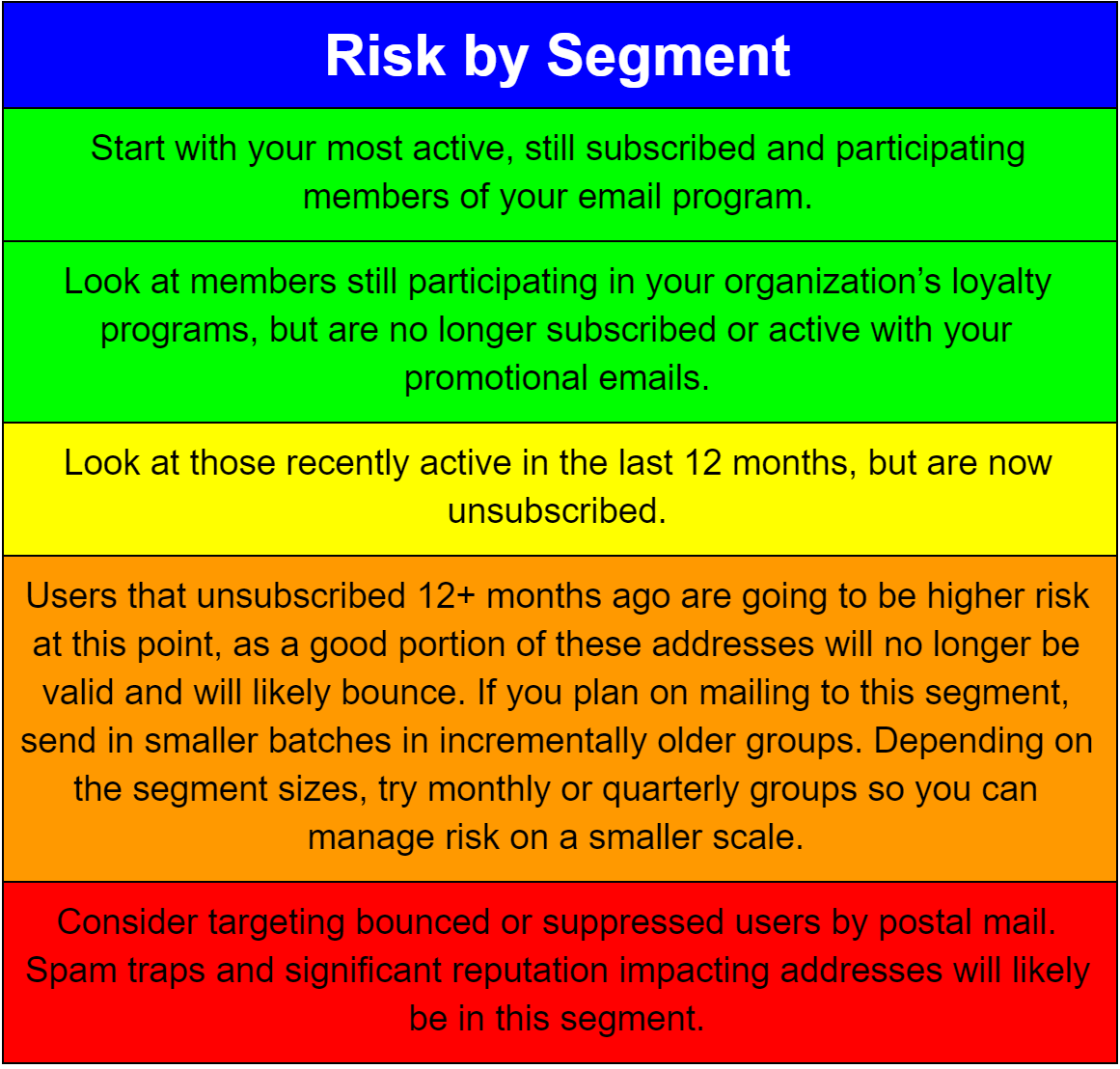
Targeting: Identify who should get notified by email and who shouldn’t. It’ll be a tough question, as you want to be efficient and coordinated but also manage risk at the same time. Look back at send your notifications in a measured approach to limit risk and reach the most engaged segments first:
Messaging: Be clear in your communications, cover what data was taken, how it was (or wasn’t) protected, when it started (if you know), and when it was secured. Also include contact information so people with questions can reach out directly, or develop an FAQ or support community to manage this incident. If relevant, also include what your business plans on doing for individuals impacted by the data breach.
Branding: Remain consistent with your existing brand consumers are used to seeing when you communicate with them. Avoid changing the friendly from to an individual’s name at this time (i.e., President Name <email@business.com>), as consumers may not recognize the name and might mistake the email as spam. To build additional trust, be sure to use a subdomain of your organizational domain, rather than a cousin domain (sub.domain.com versus email-domain.com). Include the notification email address in your public FAQ document, such as “You will receive a notification from ‘Brand Inc. <Notification@email.brand.com>’ if you’ve been affected by the breach.”
Authentication: Be sure to review your brand’s email authentication records. This should be easy if you are using a brand-specific domain for your ESP and nothing else. Confirm your SPF is set to a ~ or -all, your DKIM keys are properly configured, and if they are, look to set your DMARC records to a p=quarantine or p=reject to stop copycat notifications trying to target your brand.
List hygiene: As you approach high-risk segments, consider looking at an email hygiene service to clean the known bad names from your email list, then flag those users that have been scrubbed from the list for alternative notification methods.
Here’s some things not to do when you’re in a crisis and need to send breach notifications:
-
- Register a new domain name. New domains tend to have no brand recognition and no reputation
- Move to a new IP. New IPs need to be warmed up before being used, and this can take 30 days or more to manage
- Host your landing pages on non-secure (http://) sites: By now, the https:// secure site should be a default for all pages
- Under communicate. Be in close communication with your support teams, as they need to be equipped to answer calls, questions, and angry customers. This is something all frontline staff should be comfortable with, and a well-defined internal escalation path should be communicated to these individuals
Breaches aren’t fun by any means, but with the increasing number of breaches making the news, the corresponding number of notifications will continue to grow. Being prepared to send these notifications will become a need for businesses. Understanding the risks and the pitfalls you might face just might make getting through the process a little easier.
Also, for those out there looking at the growing number of breaches, be sure to take an inward look at your own policies and practices. Be sure to learn from the misfortune of others and take corrective actions on your networks to reduce attack surface and put controls in place to mitigate data loss/exposure.
There’s no time for regrets. You’ve just got to keep moving forward.
~ Mike McCready
Header Photo Credit:
Used under the Creative Commons Attribution License blogtrepreneur.com/tech


